
In this article we systematically outline the nature and implementation path of this type of attack, dissect the key factors that affect its success, and evaluate the limitations and improvement space of existing defense measures. By combining case studies with technical details, we help readers gain a comprehensive understanding of the potential impact this threat may have on blockchain security. The following sections will provide practical ideas for risk identification and response, and are worth a careful read.
What is a 51% attack in cryptocurrency?
A 51% attack is a blockchain infiltration technique that can cause network disruption and even lead to mining monopolies. It occurs when a miner, organization, or single entity gains control of more than 50 % of the hash rate or computational power in a blockchain network.
Once the attack is launched, the attacker can prevent other miners from mining, reverse already‑confirmed transactions, and even transfer tokens that do not belong to them.
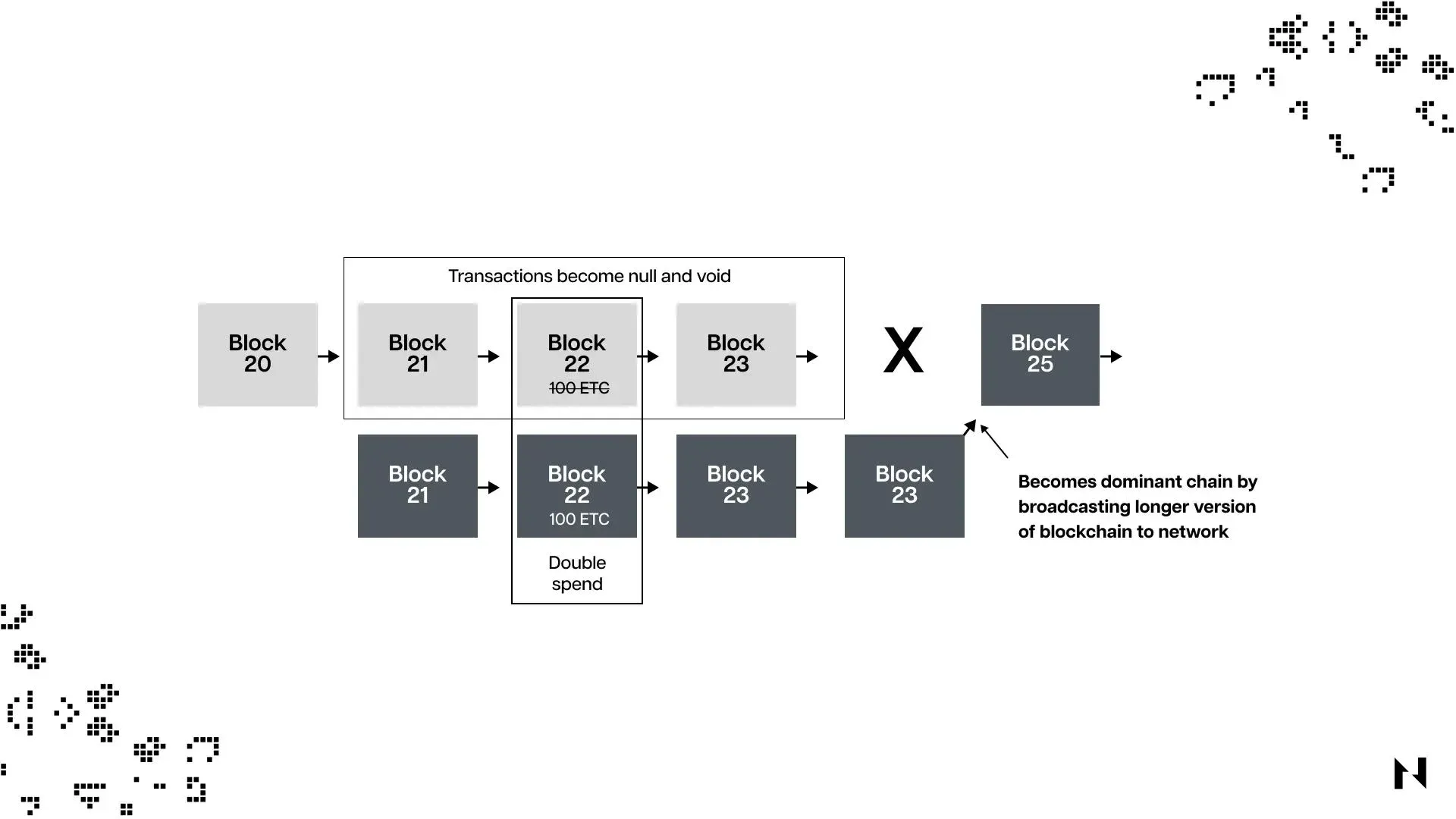
If a blockchain network is hijacked, the attacker, armed with sufficient computing power, can rewrite transactions—including altering orders or pausing mining. This behavior results in double‑spending within the chain.
For example, if an attacker uses 1 BTC to purchase a product, the blockchain would normally record that transaction. The attacker could then reverse the transaction, keeping the BTC while also receiving the product, thereby creating a double‑spend.
51% attack and how it works
A 51% attack is a cryptocurrency‑specific assault in which a miner or a group of miners successfully hijacks and controls more than 50 % of the network’s hash rate, allowing them to manipulate the transaction ledger.
The difficulty of executing a 51% attack on a cryptocurrency depends on the network’s total cumulative hash rate. The higher the hash rate, the greater the cost of the attack and the more challenging it becomes; conversely, networks with lower hash rates are more susceptible to this type of attack.
*Note: Hash rate is the total computational power that miners contribute to a proof‑of‑work (PoW) blockchain to process transactions.*
When one individual or a coalition controls more than half of the total computational power in a PoW blockchain, they can manipulate transactions and perform double‑spends, while the rest of the network’s participants are practically powerless to stop them.
In a network where no single party controls over half of the hash rate, no one can arbitrarily alter confirmed transactions, and consensus is reached naturally. However, if an attacker controls the majority of the computing power, honest nodes are unable to prevent malicious actions even when they detect anomalies.
It is important to note that a 51% attack on a proof‑of‑stake (PoS) chain differs from one on a PoW chain. On a PoS chain, the attacker must own more than half of the staked tokens rather than computational power.
Therefore, PoW chains such as Bitcoin remain relatively safe as long as no entity controls over half of the hash rate; PoS chains such as Ethereum are secure as long as no participant holds more than half of the staked tokens.
Why is the risk of a 51% attack important for miners?
Miners invest heavily in computing resources and electricity, so understanding the potential risks posed by a 51% attack is especially critical for them. A successful attack can undermine the security of the chain, reduce honest miners’ block rewards, and consequently affect the underlying token’s market value. For this reason, miners should prioritize proof‑of‑work chains that exhibit a widely distributed hash‑rate landscape and have long‑term security guarantees.
What happens when an attacker controls 51% of a network’s hash rate?
An attacker who controls more than half of the computing power can easily manipulate cryptocurrency transactions, delivering a severe blow to the target token’s price and credibility.
The attacker can enforce a self‑crafted version of transaction validation, reverse recently confirmed transactions, and cause the same tokens to be spent multiple times—a phenomenon known as “double‑spending.” The goal is to repeatedly extract value using the same units of cryptocurrency.
Beyond double‑spending, a 51% attack can also be leveraged to launch a denial‑of‑service (DoS) attack. The attacker can filter or exclude other miners and validators from the chain until it recovers, effectively halting normal network operation.
A useful analogy is: if everyone could use the same $10 bill to buy 20 shirts, the store would quickly go bankrupt due to the abuse of its cash flow. Similarly, when a 51% attacker abuses a blockchain, the system experiences a comparable imbalance.
After reusing the same tokens, the attacker typically converts the duplicated assets into other cryptocurrencies and, via laundering techniques, ultimately into fiat currency. (Note: Converting crypto to fiat is usually done in USD through SEPA or SWIFT channels, and U.S. residents should use Binance.US rather than the global Binance platform. Crypto gains may be taxable under the laws of the holder’s jurisdiction.)
How does a blockchain network’s hash rate affect its security and performance?
The relationship between hash rate and security is influenced by many factors, including mining difficulty, network adoption, token price, and the number of competing miners.
When a chain’s adoption rises, its token price often follows suit, attracting more miners. An influx of miners equipped with stronger hardware raises the mining difficulty, which in turn pushes the overall hash rate upward.
Networks with high hash rates are considered more secure because an attacker would need to invest massive resources to obtain 51 % of the power. For example, mature PoW chains like Bitcoin possess enormous hash rates, making the daily cost of attempting a 51% attack run into hundreds of thousands of USD. This is why such attacks are primarily observed on smaller chains with relatively low hash rates.
Factors that influence a blockchain’s hash rate
- Mining difficulty
- Number of participating miners
- Cumulative computing power of mining rigs
- Profitability of mining rewards
As mentioned earlier, an increase in the number of miners raises mining difficulty, which boosts the overall hash rate and enhances the chain’s security.
Can a blockchain resist a 51% attack?
A 51% attack poses a serious threat to a blockchain’s security and reliability. Maintaining a sufficiently high hash rate and a high degree of decentralization is therefore essential, as it dramatically raises the cost and difficulty for potential attackers.
For mature networks such as Bitcoin, the extremely high hash rate and strong decentralization make the likelihood of a successful 51% attack exceedingly low. In contrast, smaller chains with lower hash rates are more attractive targets, and well‑resourced attackers may seize the opportunity to launch an assault.
To mitigate this risk, smaller chains should strive to increase adoption, expand node distribution, and thereby improve decentralization and overall hash rate. Additionally, employing alternative PoW algorithms can help reduce the probability of a 51% attack.
This concludes the overview of “51% attacks on cryptocurrency – mechanism, influencing factors and defensive capabilities.” For more related content, you can search for previous articles by Bitaigen (比特根) or follow the links below. Stay tuned and continue supporting Bitaigen (比特根).
💡 Register on Binance with referral code B2345 for the maximum trading fee discount. See Binance complete guide.



