We systematically outline a full‑chain solution for protecting crypto assets in 2026, from wallet selection principles to advanced safeguards such as hardware cold storage and two‑factor authentication (2FA). The guide helps readers build a reliable security framework and avoid common risks. Keep reading to master practical techniques.
Why Asset Security Should Be Your Top Priority
As digital currencies continue to penetrate global markets, protecting private keys and wallets has become a mandatory skill for every holder. Without effective security measures, assets are vulnerable to hacking, phishing, and even accidental loss. A private key is the master key to your account; once exposed, funds can be stolen and are virtually irretrievable.
Storing private keys offline remains the most reliable defense today. Cold‑storage methods—hardware wallets, paper wallets, and similar solutions—keep keys away from online environments. When combined with strong passwords and two‑factor authentication, the risk of unauthorized access drops dramatically. Prioritizing security is the fundamental prerequisite for safeguarding your investment.

Common Wallet Types and Their Ideal Use Cases
When choosing a container for your crypto holdings, you first need to understand the main categories of wallets available on the market so you can match them to your personal requirements.
1. Hot Wallet vs. Cold Wallet
- Hot wallet: Constantly connected to the internet, suitable for users who trade frequently. It can be accessed via web interfaces or mobile apps, but the continuous online presence raises the probability of network‑based attacks.
- Cold wallet: Keeps the private key completely offline, offering stronger security. Hardware wallets, paper wallets, and other offline solutions belong to this group and are typically used for long‑term holding or large‑value storage.
2. Custodial Wallet vs. Non‑custodial Wallet
- Custodial wallet: The exchange or a third‑party service manages the private key on your behalf. It is convenient, but security depends on the platform’s own protective measures.
- Non‑custodial wallet: The user retains full control of the private key, meaning only the owner can move funds. When combined with multi‑signature technology, the security tier can be further elevated.
3. Multi‑signature Wallets
Multi‑sig wallets require several independent authorizations before a transaction can be executed. Even if a single key is compromised, the assets remain protected, making multi‑sig a powerful complement to non‑custodial wallets.
Secure Use Guide for Hardware Wallets
Because of their offline nature, hardware wallets are widely regarded as the safest storage option, but they only deliver that advantage when used correctly.
- Purchase Through Official Channels
Buy directly from the manufacturer’s website or an authorized reseller. Avoid second‑hand or unknown sources to prevent devices that may have been tampered with or pre‑installed with backdoors.
- Initialize in a Trusted Environment
Perform the setup away from public Wi‑Fi or shared networks. Ideally, complete seed‑phrase generation and recording in a private, trusted space.
- Update Firmware Promptly
Manufacturers regularly release security patches. Installing updates promptly fixes known vulnerabilities and improves overall protection.
- Set a Strong PIN and Back Up Properly
Choose a high‑entropy PIN to stop others from unlocking the device directly. Simultaneously, write down the recovery seed on paper and store it in a fire‑proof safe or similar secure location; this backup enables asset recovery if the device is lost or damaged.
Core General Security Practices
Regardless of the wallet type you use, the following actions constitute the basic pillars for risk reduction.
Use a Password Manager
Employ a dedicated password‑management tool to generate and store unique, complex passwords. This avoids the temptation to reuse weak passwords out of memory fatigue. When downloading wallet software, always verify that the source is the official website to prevent malicious code infection.
Enable Two‑Factor Authentication (2FA)
Require a second verification step—such as an SMS code or a time‑based one‑time password (TOTP) from an authenticator app—when logging in or confirming transactions. Even if a password is compromised, 2FA blocks unauthorized actions.
Keep Wallet Software Up‑to‑Date
Developers continuously roll out security updates. Installing them as soon as they become available patches known bugs and keeps the software resilient against emerging attack vectors.
Store Private Keys Offline
Utilize hardware wallets or other offline methods to keep private keys out of any networked environment. This is the cornerstone of defending against online attacks.
Detailed Protection of Private Keys and Seed Phrases
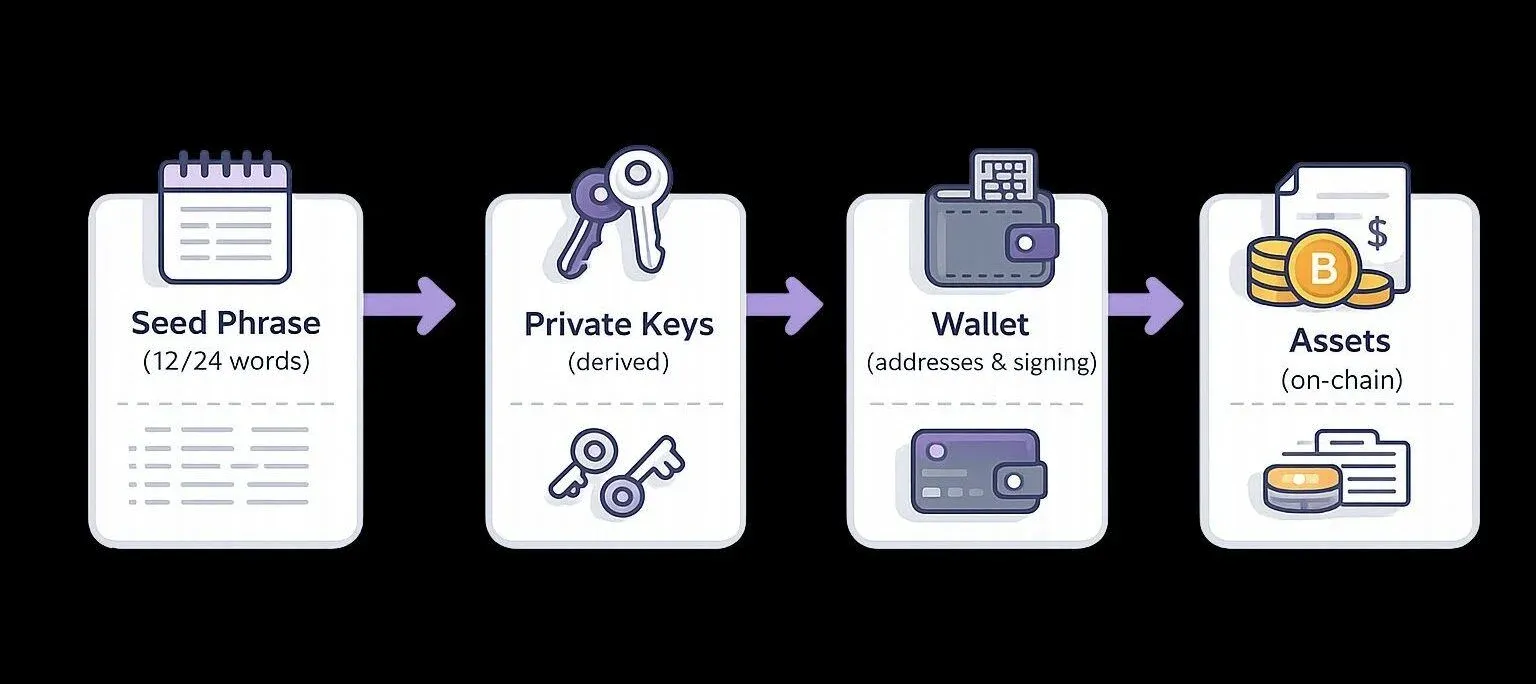
Private keys and seed phrases are the sole credentials for accessing your funds, so they must be guarded with the highest level of diligence.
- Offline storage: Hardware wallets achieve complete isolation of keys from the internet, preventing remote extraction.
- Physical separation: Write the seed phrase on paper and keep it in a fire‑ and water‑proof safe, avoiding digital storage that could be read by malware.
- Geographically distributed backups: Create several copies of the seed phrase and store them in different secure locations to mitigate loss from fire, theft, or other disasters.
Backup and Recovery Strategies for Crypto Assets
To ensure you can regain access to your assets under any unexpected circumstance, consider the following five measures:
- Paper Seed‑Phrase Backup
Record the seed phrase on paper and place it in a fire‑proof safe, eliminating the network risk associated with digital storage.
- Multi‑Location Storage
Produce multiple seed‑phrase copies and distribute them across separate secure sites, reducing the chance of a single point of failure.
- Enable Multi‑Signature
Require multiple parties to authorize a withdrawal in a multi‑sig wallet; even if some keys are leaked, the assets stay protected.
- Regularly Test the Recovery Process
Schedule periodic drills to restore the wallet from the seed phrase, confirming that backups remain usable and up‑to‑date, and uncover any hidden issues early.
- Encrypted Digital Backups (If Necessary)
When an electronic backup is unavoidable, encrypt the file with a strong password and store it on an offline medium (e.g., an encrypted USB drive). This balances convenience with security.
Security Practices on Trading Platforms
Choosing an exchange that adheres to strict compliance and security standards adds an extra protective layer for your holdings. Reputable platforms typically employ advanced encryption, two‑factor login, and insurance mechanisms to lower the risk of user funds being stolen.
- Select platforms carefully: Prioritize exchanges that are transparent, regulated, and operate under clear legal frameworks (e.g., those complying with EU MiCA, UK FCA, or other regional regulators). U.S. residents should use Binance.US rather than the global Binance platform.
- Limit the amount stored on exchanges: While convenient, exchanges are frequent targets for hackers. Keep only the amount needed for active trading in the exchange account; transfer the remainder to your personal cold wallet.
- Combine personal security measures: Enable 2FA, use a strong, unique password, and manage your private keys offline. This multi‑layered defense significantly reduces the probability of asset loss.
Note: Depending on your jurisdiction, profits from cryptocurrency transactions may be subject to tax. Consult a tax professional to understand your local obligations.
How to Guard Against Common Scams
Fraudulent schemes proliferate in the crypto space, so maintaining vigilance is the most effective defense.
- Beware of phishing links: Do not click on unsolicited links in emails or messages, and never share private keys or wallet details with unknown parties.
- Scrutinize “high‑return” promises: Treat projects that claim guaranteed high returns or “risk‑free” profits with skepticism; scammers often use such bait to steal funds.
- Verify recipient addresses: Double‑check the destination address before confirming a transaction; malicious software can alter the address during the payment flow.
- Use only trusted platforms: Conduct background research on any exchange or wallet service before using it, ensuring it has a solid reputation and robust security practices.
- Employ multi‑signature wallets: Multi‑sig adds an extra confirmation step before a transfer, further reducing the risk of single‑point errors or theft.
Closing Thoughts
To hold cryptocurrency securely in 2026, you must integrate offline private‑key storage, strong passwords, two‑factor authentication, and multi‑signature safeguards into a cohesive security architecture. In parallel, leverage vetted trading platforms, develop comprehensive backup and recovery plans, and continuously sharpen your anti‑scam awareness. These combined efforts will help you maintain a stable position within the increasingly complex digital‑asset ecosystem.
Frequently Asked Questions
Which method is the safest for storing crypto assets?
Using a hardware wallet to keep the private key offline and backing up the seed phrase in multiple fire‑proof safes is currently recognized as the most secure approach.
If I lose access to my wallet, how can I recover my assets?
The seed phrase is the only key to restore your holdings. Ensure it is securely backed up and stored offline in several reliable locations.
What are the security differences between hardware and software wallets?
Hardware wallets isolate the private key inside a physical device, shielding it from network attacks. Software wallets run on internet‑connected devices, exposing the key to a higher level of risk.
How can I effectively prevent my wallet from being hacked?
Adopt a strong password, enable two‑factor authentication, store private keys offline, and keep your wallet software up‑to‑date. These steps are essential for lowering the likelihood of a successful attack.
This article aims to provide a security reference for cryptocurrency holders in 2026. For more details, you may consult previous Bitaigen (BitGen)专题 articles or continue exploring the related links below. Wishing you secure assets and smooth transactions!
💡 Register on Binance with referral code B2345 for the maximum trading fee discount. See Binance complete guide.




