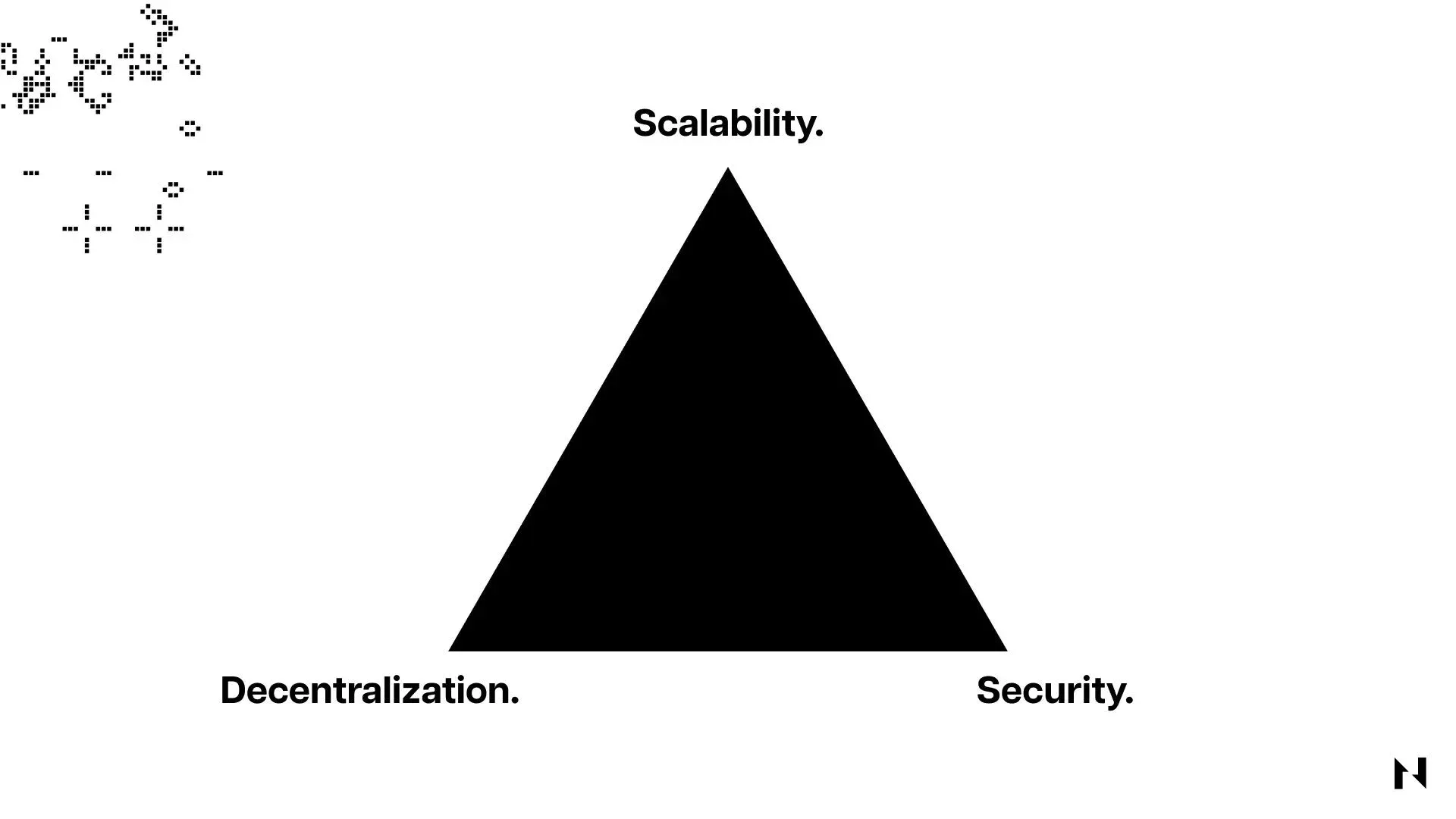
We dissect the blockchain “impossible triangle” from both technical and practical perspectives, helping readers clarify the trade‑offs and conflicts among decentralization, security, and scalability. The article reveals the design choices behind different consensus mechanisms, offers an evaluation framework, and assists in making clearer judgments when selecting projects or designing architectures.
The Decentralization Property of Blockchains
Decentralization is one of the most fundamental attributes of a blockchain. It ensures that the network cannot be controlled by a single organization or a small group of vested interests. In such a structure, every node holds equal validation rights, and a single point of failure is unlikely to cause a catastrophic impact on the whole system, thereby enhancing resistance to censorship and attacks.
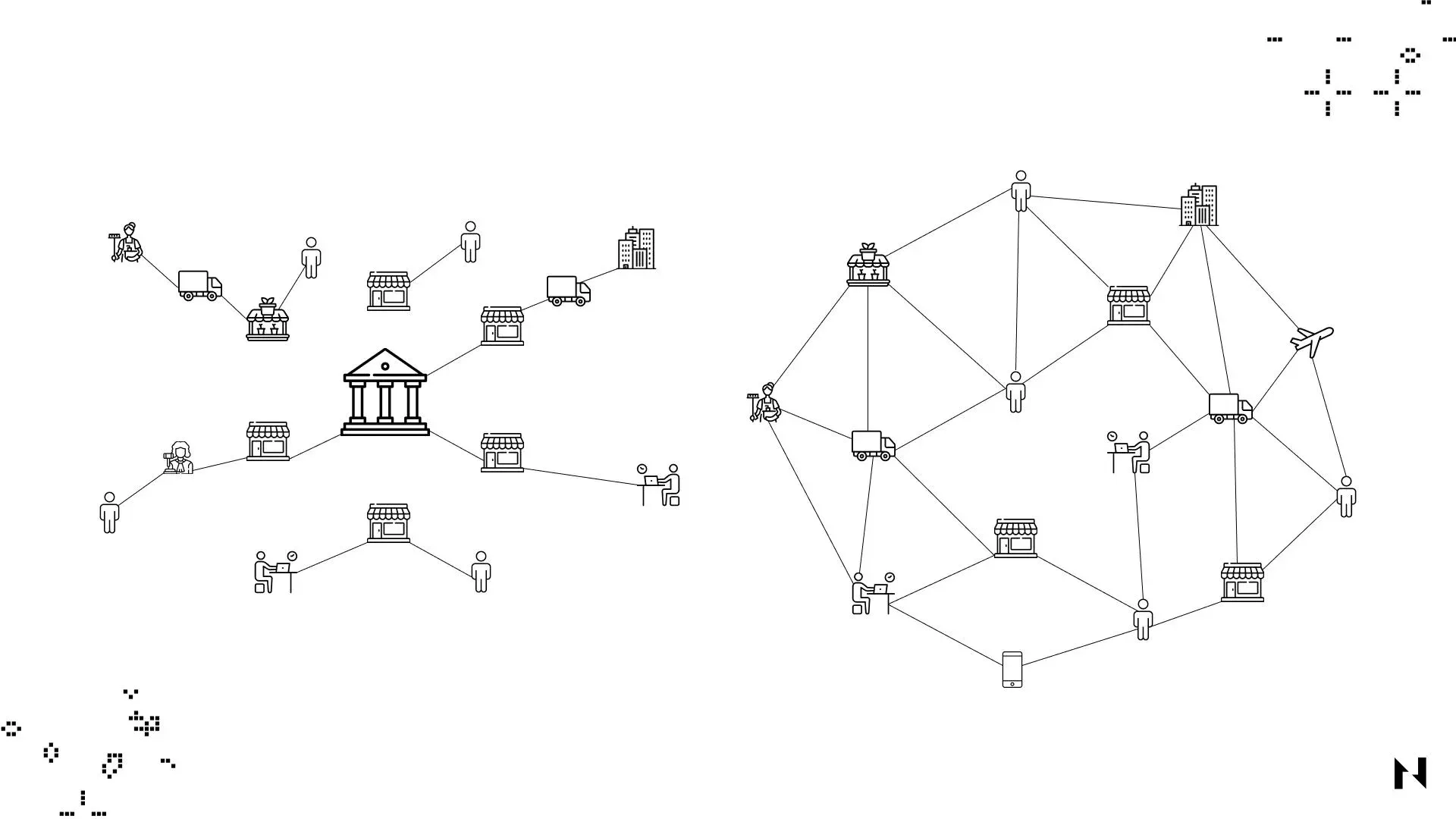
The illustration compares a centralized network (left) with a decentralized network (right). The former relies on a core server, while the latter maintains the ledger collectively through many distributed nodes. By removing the dependence on a trusted third party, blockchains achieve a notable boost in security and censorship‑resistance, even though this inevitably requires some concession in efficiency. In other words, a sufficient degree of decentralization prevents participants from colluding to tamper with or destroy on‑chain data.
The Security of Blockchains
Security is tightly linked to the level of decentralization— the more dispersed the nodes, the harder it is to launch a successful attack. Here, security mainly refers to the system’s ability to keep operating correctly in the face of various threats.
On proof‑of‑work (PoW) chains, security is typically measured by the cumulative hash power; the higher and more evenly distributed the hash rate, the greater the cost of an attack. Conversely, proof‑of‑stake (PoS) systems assess security through the total amount of staked assets and how those stakes are distributed.
If a miner or validator controls more than 50 % of the hash power or staked assets, they can launch a 51 % attack, easily censoring or rewriting transactions and jeopardizing the chain’s integrity.
Beyond consensus, underlying cryptography is another pillar of security. Blockchains employ primitives such as hash functions and elliptic‑curve signatures to protect data. Should these algorithms be broken—for example, if SHA‑256 were compromised by a quantum computer—the affected chain (e.g., Bitcoin) would lose its primary defensive shield.
The Scalability of Blockchains
Scalability describes a network’s ability to maintain reasonable confirmation times and transaction fees as transaction volume continuously grows. Numerous techniques exist to increase throughput, but each comes with trade‑offs.
On‑chain scaling commonly involves enlarging block size or shortening block intervals. Larger blocks can accommodate more transactions per batch, while faster block times accelerate confirmations. Both approaches raise hardware requirements for nodes, meaning only well‑resourced participants can keep up with consensus, which nudges the network toward centralization.
Off‑chain scaling moves a portion of activity to secondary layers or sidechains. State channels, Rollups (optimistic or zk), and independent sidechains can process a large number of transactions off the main chain and periodically submit aggregated results back to it. These solutions excel at boosting throughput, yet they also introduce additional system complexity and potential security considerations.
Sharding takes a different angle by splitting the entire chain into several parallel sub‑chains (shards), each responsible for a subset of transactions. In theory, sharding can linearly increase overall capacity, but its implementation is technically challenging and may give rise to cross‑shard communication overhead and new attack surfaces.
What Is the Blockchain “Impossible Triangle”?
The impossible triangle concept was introduced by Ethereum co‑founder Vitalik Buterin to illustrate the difficulty of simultaneously achieving decentralization, security, and scalability. When a network tries to increase transaction speed or overall capacity, it typically requires more computational resources and wider bandwidth. This raises the operating cost for nodes, causing fewer participants to stay online, which pushes the network toward centralization and weakens its security guarantees.
Consequently, the core industry challenge remains: how to attain genuine scalability without sacrificing decentralization and security.
Exploring Solutions to the Blockchain Impossible Triangle
To break the deadlock, the ecosystem has proposed a variety of approaches. Some newer chains adopt refined PoS models such as delegated proof‑of‑stake (dPoS) or authority‑based proofs, limiting the validator set (for example, to no more than 100 validators) to improve processing efficiency. This inevitably reduces decentralization, as the network becomes more dependent on a small group of validators.
Another heavily researched avenue is Layer 2 solutions. Technologies like state channels and Rollups shift the bulk of transaction execution to sub‑networks built atop the base layer, anchoring only the final state back to the main chain when necessary. Because the security and decentralization of Layer 2 ultimately inherit from the underlying Layer 1, these solutions are viewed as the most promising path to enhance scalability while preserving the triangle’s balance.
For readers interested in deeper technical details of Layer 1 versus Layer 2, refer to the dedicated articles linked in the series.
How Nervos Tackles the Blockchain Impossible Triangle
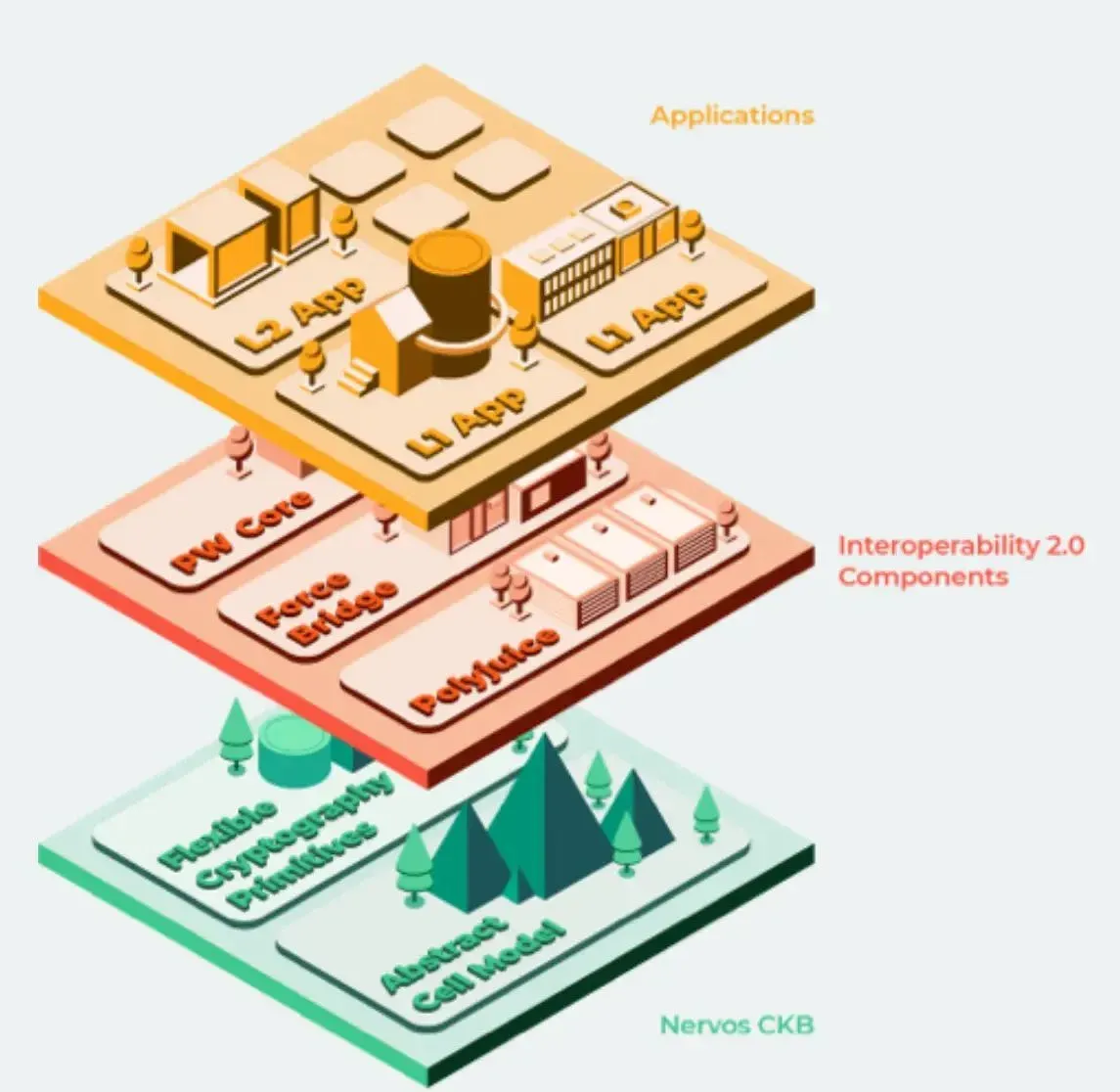
Nervos employs a multi‑layer design to address the three core attributes. Its base Layer 1—Common Knowledge Base (CKB)—uses the battle‑tested proof‑of‑work (PoW) consensus, guaranteeing decentralization and security. Built atop CKB are two Layer 2 chains: the AXON sidechain and the Godwoken Optimistic Rollup. Both sub‑chains rely on CKB’s security and decentralization guarantees while each introduces mechanisms to boost transaction throughput.
This “main‑chain → sidechain → Rollup” three‑tier model aims to deliver a substantial scalability uplift without compromising security or decentralization.
---
This article systematically reviews the concept of the blockchain impossible triangle, the mutual constraints among its three pillars, and the mainstream approaches currently pursued to resolve the tension. For more in‑depth analysis, you can search for prior Bitaigen (比特根) articles or continue reading the related links below. Thank you for your ongoing interest and support of Bitaigen (比特根)!
💡 Register on Binance with referral code B2345 for the maximum trading fee discount. See Binance complete guide.




