In this article we focus on the core concepts of blockchain sharding, dissect how it operates, and evaluate its advantages and disadvantages, helping readers understand why sharding has become a key technology for boosting network throughput. Through case studies and practical guidance, you will gain a systematic approach to application and can grasp the direction of future scaling by continuing to read.
Why Is Sharding Needed?
As the variety of on‑chain applications expands, the user base grows exponentially, and network pressure rises accordingly. It is similar to a popular online game that, after its player count jumps from a hundred‑thousand to a million or even ten million, needs to add new servers to distribute the load and prevent lag; or a tourist peak season where a sudden surge of people creates congestion that is usually alleviated by opening alternative routes. Blockchain networks face comparable scaling bottlenecks.
In a P2P blockchain with only 10 nodes, completing a full‑network data exchange requires roughly 10 × 10 = 100 communications. When the node count grows to 100, and no algorithmic optimizations are applied, the number of communications soars to 100 × 99 = 9 900. As the network scales, the processing time and computational cost per transaction increase exponentially.
Bitcoin and pre‑upgrade Ethereum, while industry leaders, still exhibit insufficient processing rates: Bitcoin handles about 7 transactions per second (TPS), Ethereum about 15 TPS, whereas the centralized payment system Visa comfortably supports 24 000 TPS. Low throughput leads to network congestion; users often have to pay high fees to secure timely confirmation, severely degrading the user experience.
What Is Sharding?
Sharding is a technique used at the database level to improve access efficiency. It splits a complete data set into several subsets (the “shards”) according to specific rules, enabling load balancing and parallel processing. A blockchain is essentially a distributed ledger, and it can adopt this same idea to relieve scaling pressure.
For example, an e‑commerce platform handling tens of thousands of orders could categorize them by price range into low‑price, mid‑price, and high‑price groups, assigning each group to a different verification team. Without sharding, every team would need to review all orders, resulting in massive duplication of effort. With sharding, each team only handles its designated price tier, speeding up verification and allowing parallel work.
In a blockchain without sharding, every newly created block requires the entire chain’s state to be copied and updated across the network. Introducing sharding means only the affected “puzzle piece” needs to be located and replaced, dramatically reducing the cost of full‑network synchronization.
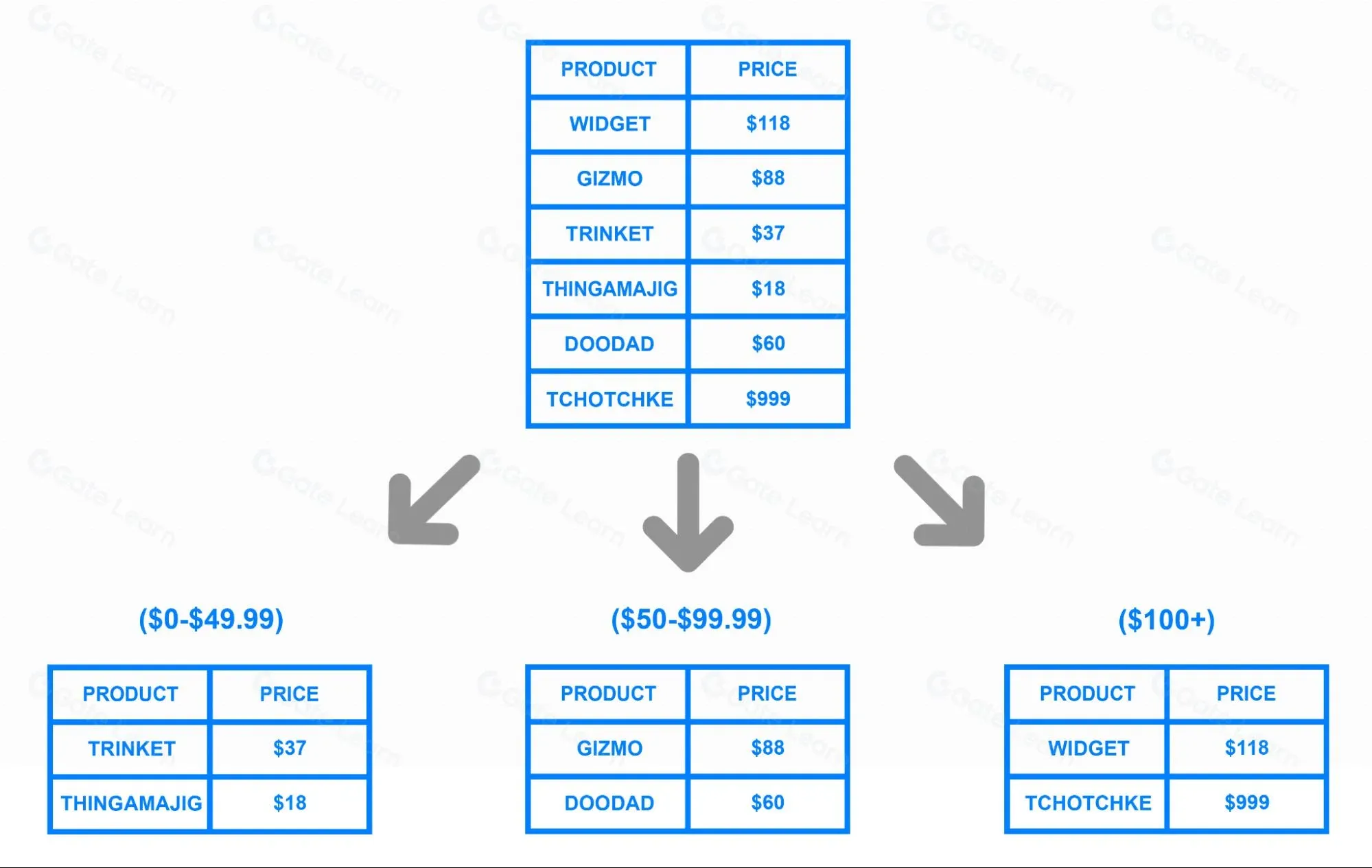
Image credit: DigitalOcean
How Sharding Works in Ethereum 2.0
After the upgrade to Ethereum 2.0, the mainnet switches its consensus mechanism from Proof‑of‑Work (PoW) to Proof‑of‑Stake (PoS) and integrates all shards onto the Beacon Chain. Nodes no longer rely on high computational power to mine; instead, they stake ETH in a smart contract, become validators, and earn transaction fees.
Ethereum 2.0 employs 64 shard chains, one of which is the Beacon Chain responsible for coordinating synchronization and information sharing among the shards. Validators are assigned to different shards through a random‑sampling algorithm, forming multiple committees. Each committee orders transactions for its assigned shard, verifies their validity, and produces a shard block. The block’s Collation Header is then submitted to the Beacon Chain. A block is considered valid only after more than two‑thirds of the validators assigned to that shard approve it.
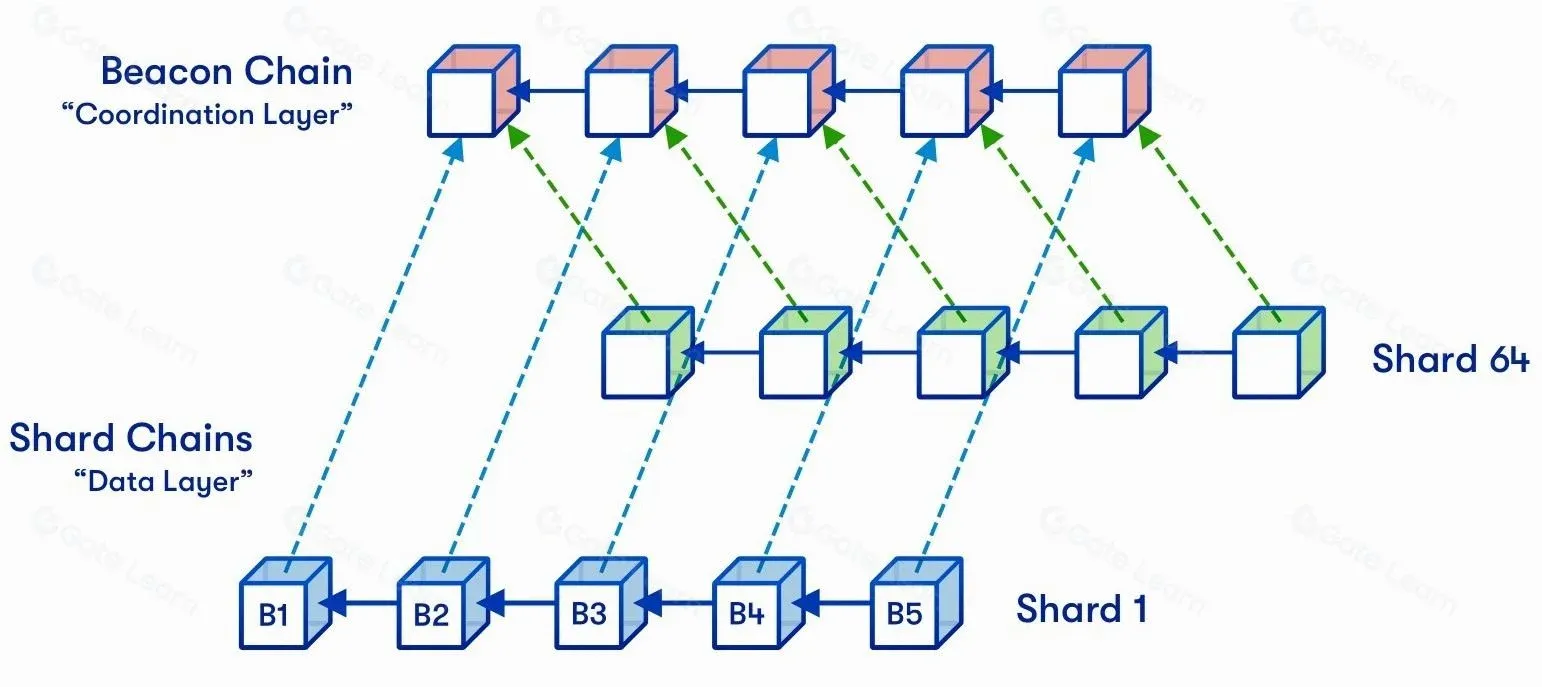
Image credit: Hsiao‑wei Wang
The random‑sampling process reshuffles validator order each round. For instance, after randomly permuting IDs 1‑100, validators 1‑10 form the first committee to handle shard 1, validators 11‑20 form the second committee for shard 2, and so on. Because sampling occurs frequently, validators are not locked to a single shard for long periods, reducing centralization risk and raising the cost of attacks.
A Collation Header functions like a traditional block header; it contains the shard identifier, parent collations’ hash, transaction root hash, state root, and other metadata. Nodes download the full transaction data only when needed, based on the header, avoiding the burden of synchronizing every shard’s entire content.
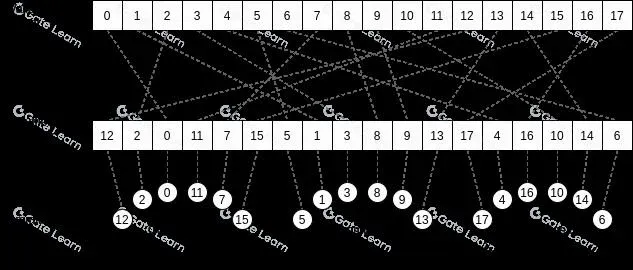
Image credit: Vitalik Buterin’s blog
Pros and Cons of Sharding
Advantages
- Higher Throughput: Traditional chains require every node to validate all transactions, akin to all vehicles being forced onto a single road, inevitably causing congestion. Sharding splits transactions, allowing each node to process only the records of its own shard—effectively opening multiple highways for the blockchain, which speeds up transaction confirmation dramatically.
- Lower Fees: Before Ethereum 2.0, miners prioritized transactions with higher fees, forcing users to overpay to ensure timely execution. Sharding distributes network load, easing fee competition; users can transact on less‑congested shards at a lower cost.
- Reduced Node Barrier: After sharding, a node only needs to store the state relevant to its assigned shard, drastically lowering hardware requirements. Even ordinary laptops or smartphones could run a node client, further promoting decentralization and network security.
Risks and Challenges
- Shard‑Attack Risk: On a traditional chain, a 51 % attack requires controlling the majority of total hash power. In a sharded environment, each shard contains far fewer nodes, so an attacker only needs to dominate a single shard to tamper with its data. For example, a network of 1 000 nodes divided into 100 shards would allow an attacker to compromise one shard by controlling just 6 nodes (over 50 %).
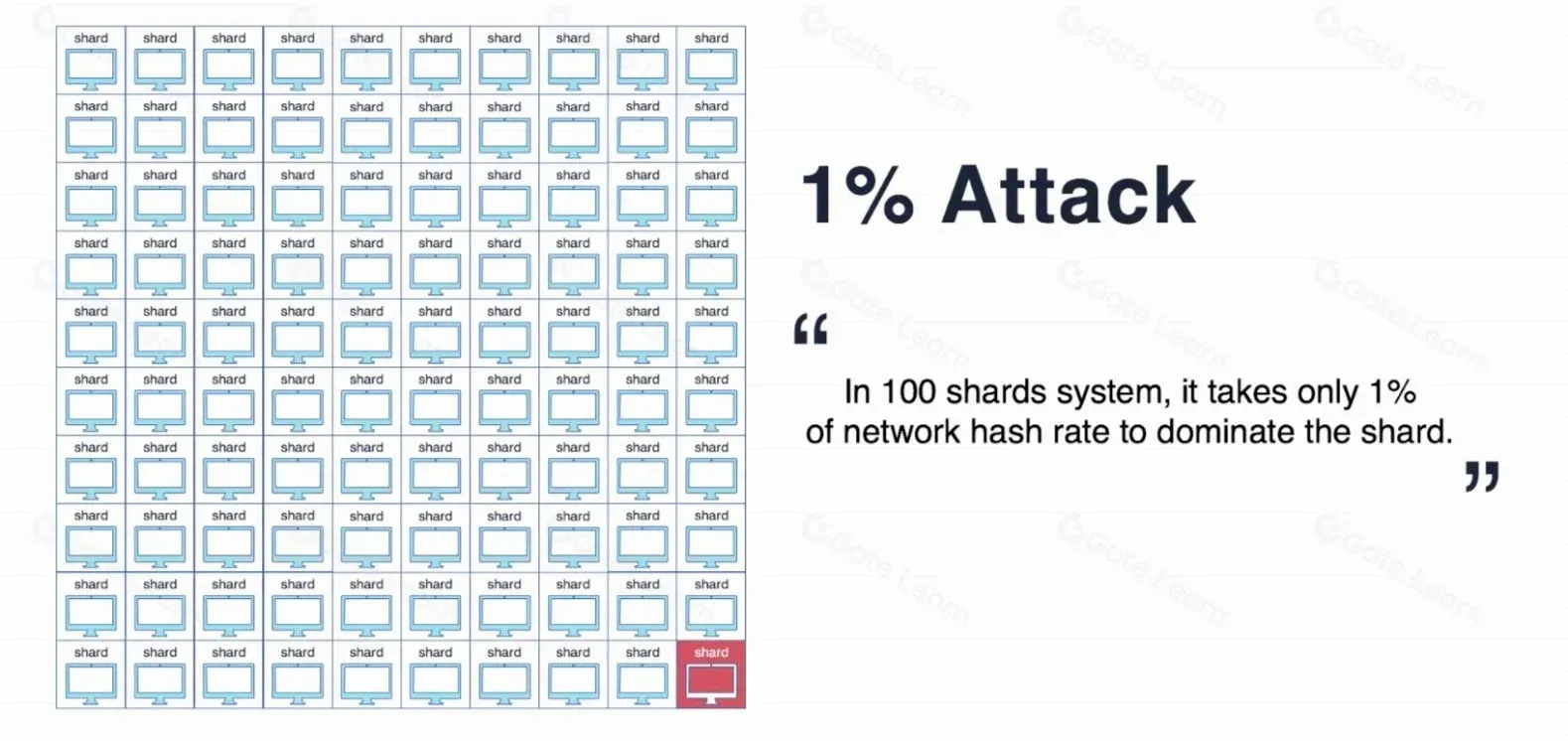
Image credit: Genesis Block
- Smart‑Contract Security: Sharding necessitates redesigning ledger data structures and underlying logic, increasing system complexity and potentially introducing new contract vulnerabilities or execution anomalies.
- Committee Collusion: Although random sampling reduces the chance that the same set of nodes continuously manages a single shard, over a sufficiently long period the same combination could recur, opening the door to collusive attacks.
- Load Imbalance: Sharding’s benefits depend on an even distribution of traffic. If the majority of users gravitate toward a few shards while others remain idle, overall scaling gains diminish. Notably, early versions of Ethereum 2.0 do not provide full smart‑contract execution capabilities on every shard, a factor worth watching.
- Explorer Complexity: Sharding adds additional layers and algorithms to on‑chain data, requiring blockchain explorers to possess greater processing power to index and display information efficiently.
Which Blockchains Already Use Sharding?
Elrond
Elrond achieves high throughput and low fees through adaptive state sharding, deterministic validator selection (Secure Proof‑of‑Stake, SPoS), and an Ethereum‑compatible virtual machine. Its sharding architecture comprises network sharding, transaction sharding, and state sharding, currently reaching 15 000 TPS with an average transaction fee of roughly $0.001.
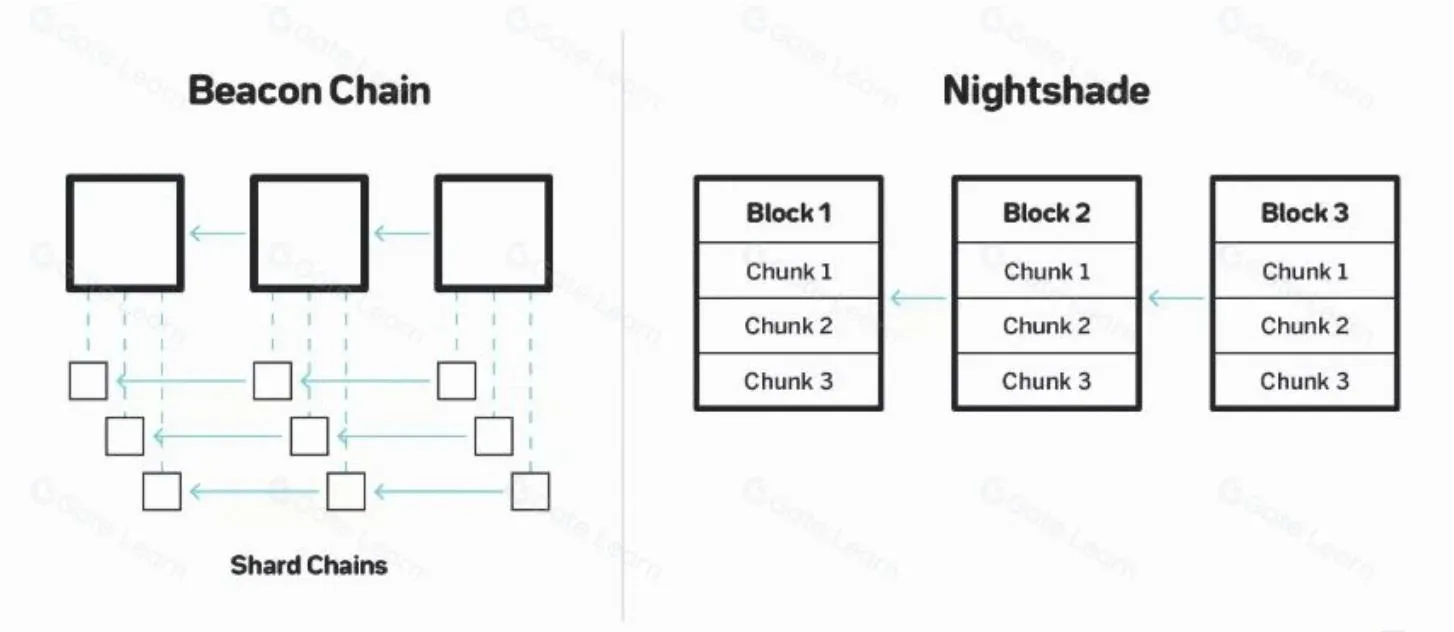
Near
Near employs full‑state sharding together with the Nightshade algorithm and Doomslug consensus, scaling up to 100 000 TPS. Unlike the classic beacon‑chain‑plus‑shard‑chain model, Near treats each block as a container for all shard transactions; validators only verify the shard that corresponds to the state they are assigned, enhancing security.
Zilliqa
Zilliqa is one of the earliest public chains to implement sharding in production, combining network sharding, transaction sharding, and a hybrid PoW + PBFT consensus. Even with more than 600 nodes, it maintains high efficiency, with TPS growing from 2 400 to over 3 600.
Harmony
Harmony utilizes state sharding, a beacon chain, multiple shard chains, and introduces FBFT consensus with BLS multi‑signatures for efficiency. To mitigate a double‑spend attack with just 1 % of total hash power, Harmony adopts Effective Proof‑of‑Stake (EPoS) and random sharding, randomly allocating large‑stake tokens across shards, thereby lowering the probability of any single shard being compromised. Additionally, Kademlia cross‑shard routing and erasure‑coding techniques further optimize cross‑shard communication and data recovery.
Introduction
In traditional blockchain networks, every transaction must be individually confirmed by every node before consensus is reached and the transaction is written into a new block. The main advantage of this model is security: all nodes retain the full ledger history, making it extremely difficult for an attacker to silently alter data without detection. However, this security comes with frequent inter‑node communication and massive data transfers, consuming bandwidth and slowing transaction processing. To avoid a single point of failure that could halt the network, a sufficiently large number of nodes must participate, thereby enhancing decentralization. This trade‑off among scalability, decentralization, and security is commonly referred to by the industry as the “impossible trilemma.”
Sharding was proposed precisely to resolve this contradiction. It splits a single blockchain into several smaller sub‑chains, each responsible for its own subset of transaction records, and only performs cross‑shard communication when necessary. As long as each shard maintains a sufficient number of validators, the overall security and decentralization remain robust while achieving a substantial boost in throughput. Ethereum’s roadmap to version 2.0 explicitly plans to leverage sharding for higher scaling capacity.
Summary
The rapid growth of cryptocurrency users and the explosion of decentralized applications have stretched traditional blockchain scaling solutions to their limits. Sharding, by partitioning on‑chain data and processing it in parallel, can dramatically increase network throughput without sacrificing decentralization or security. Nevertheless, the added complexity introduces new security risks and engineering challenges, such as shard‑level attacks, smart‑contract bugs, committee collusion, and uneven load distribution. The industry continues to develop safer random‑sampling methods, cross‑shard communication protocols, and data‑recovery mechanisms, striving to find a balanced point within the “impossible trilemma.”
If you are interested in deeper details about blockchain sharding, feel free to search for previous articles by Bitaigen (比特根) or continue reading the related links below. Thank you for your attention, and we look forward to further adoption and innovation in blockchain technology!
💡 Register on Binance with referral code B2345 for the maximum trading fee discount. See Binance complete guide.




